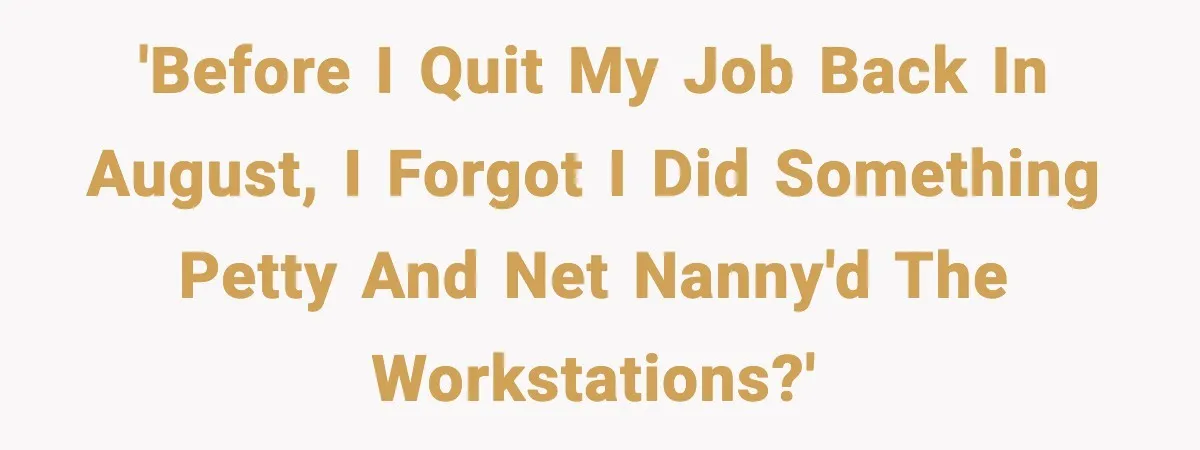
One employee walked out of his job, but the real story started months later.
Sometimes workplace revenge does not explode in a dramatic confrontation. Sometimes it hides quietly inside a system setting, waiting to confuse people long after the person who made the change has moved on.
That is exactly what happened in this Reddit story.
The poster worked closely with the IT department at a manufacturing site that relied heavily on secure networks because of government contracts. Over time, he earned trust from the cybersecurity team and even received administrator credentials to help troubleshoot workstations when IT staff were overwhelmed.
Then the company culture started to wear him down.
Management treated IT like an obstacle instead of a partner. Employees ignored policies. Systems stayed unlocked. And some workers spent plenty of time watching cable news on company computers.
On the day he left the job, the poster discovered a workstation left open and blasting political news during work hours.
That moment sparked an idea.
Now, read the full story:
 Honestly, reading this story gives off a mix of amusement and mild disbelief.
Honestly, reading this story gives off a mix of amusement and mild disbelief.
On one hand, the poster did not break machines, delete files, or sabotage operations. He simply restricted access to websites that employees were already warned not to use during work hours.
On the other hand, it shows how fragile workplace systems can be when security policies are ignored. Shared admin passwords, unlocked workstations, and missing monitoring tools create an environment where small actions ripple for months.
This situation is less about politics and more about workplace behavior. When people treat security policies like an inconvenience, they open doors for exactly this kind of mystery problem.
Stories like this highlight two major workplace issues. The first is cybersecurity discipline. The second is workplace culture around technology use.
In this case the technical problem jumps out immediately. The poster described a system where administrator credentials were shared among multiple users and not tied to an individual account.
Cybersecurity professionals consider that practice extremely risky.
The National Institute of Standards and Technology warns that shared administrative accounts create major security gaps because they remove accountability. When multiple users share the same credentials, investigators cannot trace actions back to a specific person.
That issue appears throughout the story. The poster mentioned shared passwords, unlocked machines, and minimal monitoring tools.
Those conditions are often referred to as “weak access control environments.” In those environments even well intentioned employees can make changes that go unnoticed for months.
Another problem involves unattended workstations.
Cybersecurity guidance from the Cybersecurity and Infrastructure Security Agency recommends locking computers whenever employees leave their desks. Unlocked workstations expose companies to data breaches, malware installation, and unauthorized changes.
In the story, employees repeatedly ignored this rule. That behavior likely made the poster’s actions possible in the first place.
The second theme involves productivity and internet use at work.
Many companies block entertainment or news websites to reduce distractions. A report by Salary.com found that roughly 64 percent of employees admit visiting non work related websites during the workday.
That behavior becomes more common when supervision is low or workplace culture tolerates it.
Employers often respond by installing website filtering systems. These systems restrict access to categories such as social media, streaming platforms, or news sites depending on company policy.
From a management perspective, filtering tools aim to reduce lost productivity and network risks.
From an employee perspective, those restrictions can feel overly strict if they appear selective or inconsistent.
Another lesson here involves how companies treat their IT departments.
Research from Deloitte shows that organizations with strong collaboration between leadership and IT teams tend to experience fewer operational disruptions and security incidents.
When IT teams lack resources or respect, small technical problems often grow into larger ones.
The Reddit story demonstrates that dynamic clearly. Management reportedly ignored IT recommendations, minimized budgets, and forced staff to work excessive hours.
That environment likely contributed to weak security controls.
In the end the poster’s prank exposed several vulnerabilities. Shared credentials, lack of monitoring, and unlocked machines all created an environment where a simple settings change went unnoticed for months.
Security experts usually recommend three straightforward improvements.
First, assign unique administrator credentials to each authorized user.
Second, enforce automatic screen locks to prevent unauthorized workstation access.
Third, monitor network changes through logging systems that identify who modified settings and when.
These basic practices help prevent both malicious activity and accidental misconfigurations.
Workplace pranks sometimes reveal hidden weaknesses.
This story offers a perfect example.
Check out how the community responded:
Many commenters loved the quiet chaos of the situation. They saw the website blocks as harmless revenge that also forced employees to actually focus on their jobs.
Other users shared similar workplace pranks involving blocked channels or restricted content. Apparently “stealth tech fixes” happen more often than people think.
A few commenters pointed out the glaring cybersecurity problems in the story. Shared administrator passwords made several people cringe immediately.
This story blends workplace humor with a serious lesson.
At first glance it looks like harmless petty revenge. One employee quietly blocks a few distracting websites before leaving the company, and the problem confuses everyone months later.
But underneath the humor sits a deeper issue.
Organizations that ignore IT departments and treat cybersecurity rules as optional create fragile systems. Shared passwords, unlocked machines, and missing monitoring tools allow tiny changes to ripple through entire networks.
The Reddit poster did not crash servers or sabotage equipment. He simply used existing permissions in a system that lacked oversight.
Sometimes those small acts expose larger weaknesses.
So what do you think? Was this clever harmless payback, or did the employee cross a line by making changes before leaving? And if you discovered a mysterious “glitch in the Matrix” at your workplace, how long do you think it would take to solve it?